Due to WordPress’s popularity, it is one of the most targeted content management systems for brute force attacks. Recent studies have even shown that WordPress is powering 34% of all the websites worldwide! Not using WordPress? Not to worry, this method can be used for any file or directory that needs to be protected.
What is a brute force attack?
A brute force attack (also known as an exhaustive search), is a cyberattack that guesses a username/email and password combination until a valid login is discovered. This process is done with an automatic script. The hacker simply needs to set up a database that is capable of continually guessing combinations.
WordPress is pretty safe, so why do we need protection?
The core of WordPress is safe because it’s actively maintained by people around the globe, but people around the globe also hide their front door keys under their doormat. If the key (weak password) is easy to find, then it doesn’t matter how strong your lock (login form) is.
Plugin Protection
There are a few plugins that can help protect your WordPress site from brute force attacks.
These plugins can block users after several failed logins attempts, add reCAPTCHA to login forms and have the ability to Blacklist/Whitelist IP addresses. While installing one of these plugins will help protect your website, it isn’t the ideal solution. If coding is your game, there is a more efficient way…
Protection without plugins
Here at Digital Noir, we keep our WordPress websites light by keeping the number of installed plugins to a minimum as they can drain server resources. We can do this by creating rules on the .htaccess file. The idea behind this is to add an extra layer of security before you reach the WordPress login screen by using a password-protected file. This method is called .htaccess authentication.
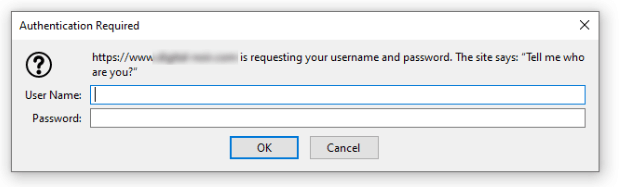
This extra login step may be a little bit annoying to some users, but trust us – your server will thank you! This authentication appears before the request even reaches your server resources, so your CPU won’t suffer when your site is attacked by 500 login requests from different IP addresses at once.
Firstly, you’ll need to create a username and password, they can be as simple as you like. Remember we only want to prevent brute force attacks at the WordPress login. The automated script can’t brute the .htaccess authentication login.
Let’s say the username is: frankly and the password is: notbot
We need to ‘hash’ the password and create a .htpasswd entry, this can be easily generated by using this online tool. ‘Hashing’ the password will covert it into unreadable strings of characters that are designed to be impossible to convert back.
Your .htpasswd entry should look something like this:
frankly:$apr1$8k9QqZWX$d8b/DfqwV81jm5on7wAS50
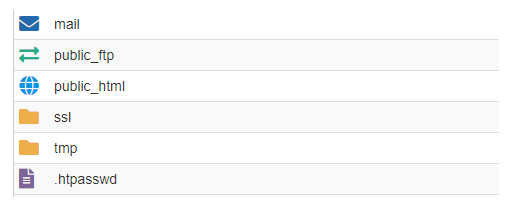
In your hosting, create a new file called .htpasswd with the .htpasswd entry inside and place it into your root folder (the same folder that contains public_html).
Now it’s time to edit the .htaccess file on your WordPress installation folder (if you install WordPress in the root then its located in public_html folder). Add the following line of code, but make sure to change the path of the htpasswd file to the correct path location.
# Minimal Forbidden Page ErrorDocument 401 "Unauthorized Access" ErrorDocument 403 "Forbidden" # Protect wp-login.php AuthUserFile /home/yourhostingusername/.htpasswd AuthName "Tell me who are you?" AuthType Basic require user frankly
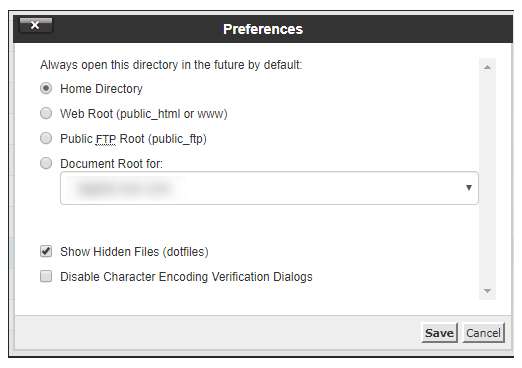
Note: .htaccess and .htpasswd can sometimes be hidden from the file list, you will need to change the file manager preferences to show hidden files
That’s it! This is my favourite method of protecting WordPress sites from brute force attacks. By using this method, we have dropped password guessing requests from 100 attacks a minute to zilch on some of our client sites!
Need some help with your website security? Get in touch.